Blockchain Dictionary
Access Control
Policies and technical controls that define who can access critical systems, keys, and infrastructure.
Address
A unique blockchain identifier used to send and receive digital assets.
Alerting
Automated notifications triggered when systems exceed thresholds or encounter failures.
AMM
An automated market maker that uses liquidity pools and formulas instead of traditional order books.
Appchain
A blockchain designed specifically for a single application, ecosystem, or business model.
Arbitrage
A trading strategy that captures price differences for the same asset across markets or venues.
Archive Node
A node that stores the complete historical blockchain state, enabling deep historical queries.
Bandwidth
The amount of data that can be transmitted over a connection in a given time.
Bare Metal RPC
RPC infrastructure deployed on dedicated physical servers for predictable performance and lower latency.
Bare Metal Server
A dedicated physical server used for predictable, high-performance workloads without shared virtualization overhead.
Block
A bundle of validated transactions that is added to the blockchain ledger.
Block Height
The position of a block within the blockchain, measured by the number of prior blocks.
Block Time
The approximate time a blockchain network takes to produce a new block.
Blockchain
A distributed ledger system that records transactions across a network of computers in a verifiable way.
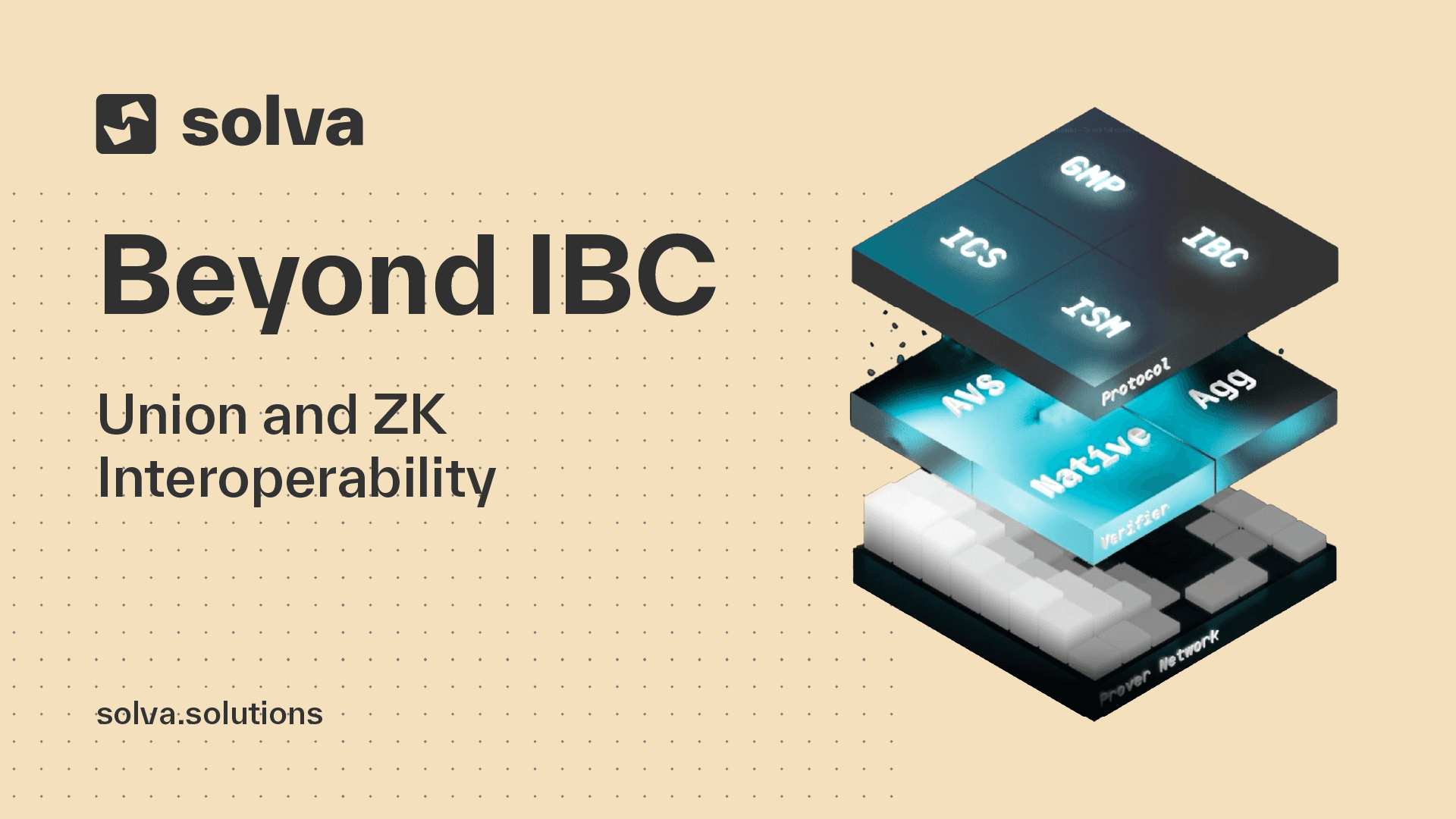
Bridge
Infrastructure that allows assets or messages to move between blockchains.
Business Staking
Staking solutions tailored to companies, protocols, and organizations managing digital asset treasuries.
Chain Abstraction
An approach that hides chain-specific complexity from users or applications across multiple networks.
Chain Development
The design and implementation of a custom blockchain network, including architecture, modules, and launch setup.
Chain Endpoint
A direct connection point to blockchain infrastructure used for reading state or submitting transactions.
Chain Maintenance
Ongoing operational work required to keep a blockchain healthy, upgraded, and available.
Security Standards
Fault-tolerant systems built for predictable operation and continuous availability


We are strictly adhering to SOC2 standards, and are currently in the process of getting our certification.

Defense-in-depth across all system layers. MPC-based signing and industry-standard key management secure signing workflows.

Redundant geographic deployments with hot failover ensure deterministic behavior during network or platform events.

Least-privilege access controls, encrypted end-to-end communications, and VPN-based isolation protect all components.